The Demonstration
Veritasium's Derek Muller published a video this week showing cybersecurity researchers draining $10,000 from MKBHD's fully locked iPhone using off-the-shelf NFC hardware, a laptop, and a Python script. No passcode entered. No Face ID prompt. No unlock of any kind. The phone sat on a reader, the screen stayed dark, and $10,000 moved.
https://www.youtube.com/watch?v=PPJ6NJkmDAo&embedable=true
The researchers — Professors Ioana Boureanu from the University of Surrey and Tom Chothia from the University of Birmingham — walked through the full attack chain live on camera. They started with a $5 test charge to confirm the relay was working, then scaled up to $10,000 in a single transaction.
The Threads reaction was immediate. As one tech creator put it:
"Veritasium dropped a video that should honestly scare anyone with an iPhone. They teamed up with MKBHD to prove you can steal $10,000 from a locked phone without ever touching the screen or using FaceID. It's not a theoretical bug; they actually did it."
Others were more measured:
"Apple says it's Visa's problem, Visa says it's too rare to matter, and consumers will just get refunds. Maybe it's too rare to fix, but I'm not taking a gamble on the refund."
Is This A New Issue?
Technically? No. And that’s the scary part.
This vulnerability was first disclosed in 2021 by the same researchers, presented at the 2022 IEEE Symposium on Security and Privacy, and demonstrated on camera with a £1,000 transaction. The attack mechanism hasn't changed. The conditions haven't changed. The fix status hasn't changed.
What's new is the scale of the demonstration and the audience. Veritasium has 16 million subscribers. MKBHD has 20 million. Putting the two biggest science and tech YouTubers in the same room, on camera, draining $10,000 from a locked device — that's not a conference talk. That's a pressure campaign.
The exploit itself works like this: Apple's Express Transit mode lets you tap your iPhone at a subway turnstile without unlocking it. That's the feature — speed over security for small transit payments. The problem is that the iPhone trusts a flag from the NFC reader that says the transaction amount is small. It doesn't actually verify the amount. A man-in-the-middle device spoofs the transit terminal identifier (researchers call these the "magic bytes"), intercepts the NFC handshake, flips the relevant protocol bits, and relays the Visa credentials to a real payment terminal that processes whatever amount the attacker wants.
The attack chain requires: physical proximity to the victim's iPhone (about four inches), a Proxmark NFC reader, a laptop running relay software, and an NFC-enabled Android phone acting as a card emulator at the real terminal. The victim must have Express Transit enabled with a Visa card specifically. It doesn't work with Mastercard, Amex, or Discover. It doesn't work with Samsung Pay.
Why Should Developers Care About This
If you build anything that touches mobile payments, NFC, or trust boundaries in contactless protocols, this is a case study worth dissecting.
The core engineering failure is a trust-boundary violation. The iPhone's Secure Element trusts that an NFC reader is telling the truth about the transaction type and amount. The phone reads a flag and believes it. It doesn't independently verify the amount against the payment network before authorizing the transaction. For Express Transit, this was a deliberate design choice — transit gates need sub-second response times, so Apple skipped the verification step. The researchers demonstrated that this trust assumption is exploitable.
The protocol-level issue is specific and fixable. The original research paper identified exactly where the fix should go: either Apple should refuse to authorize Express Transit transactions above a threshold without user confirmation, or Visa should add server-side checks that flag transit-mode transactions above typical fare amounts. Neither change is architecturally complex. Neither has been implemented in five years.
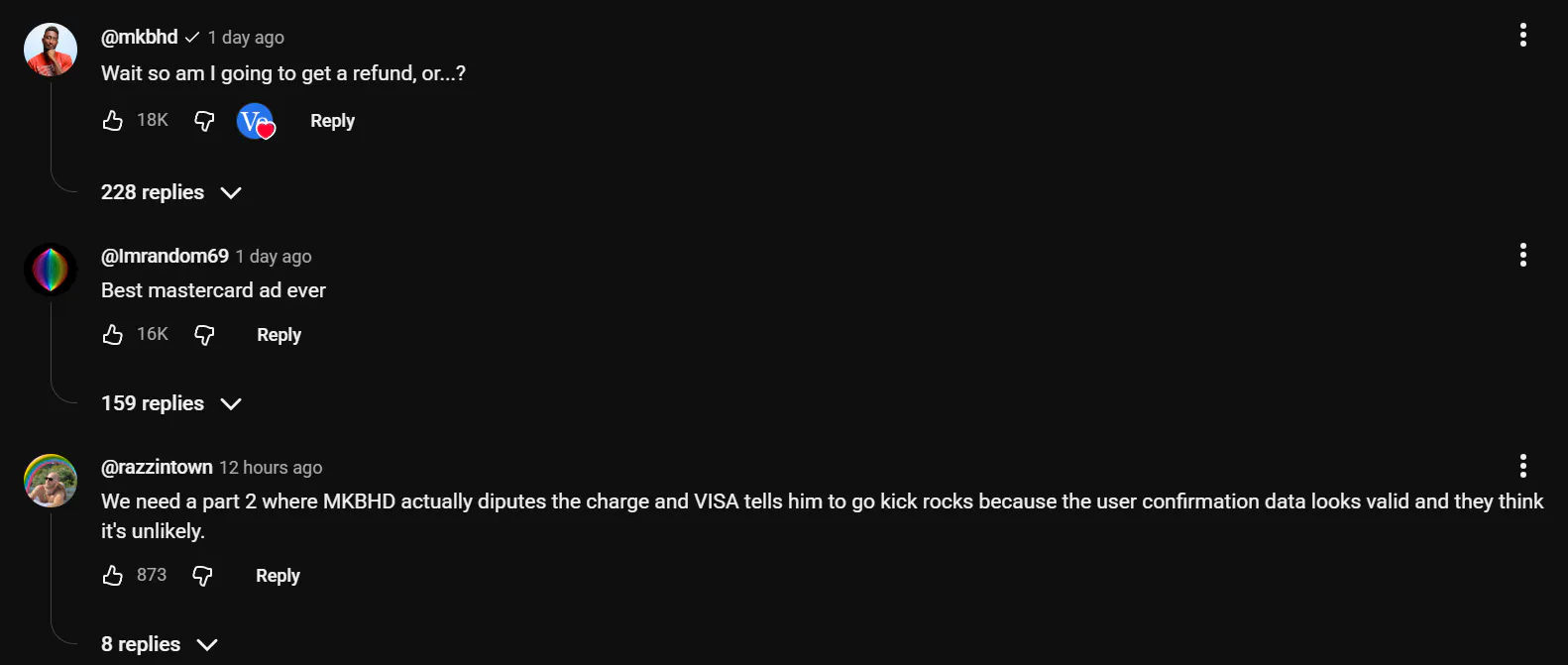
The finger-pointing is the real story. Apple told Veritasium the issue lies with Visa's system. Visa said the attack is "very unlikely" in real-world settings and that cardholders are protected by a zero-liability policy. The original lead researcher, Dr. Andreea Radu, nailed the dynamic back in 2021: "When two industry parties each have partial blame, neither is willing to accept responsibility and implement a fix, leaving users vulnerable indefinitely."
That quote is five years old. Nothing has changed.
What's Questionable or Unclear
Before you panic and disable Apple Pay entirely, some context matters.
This attack is hard to pull off at scale. You need physical proximity for several seconds — not a brush-past in a crowd, but sustained contact with a reader while the relay completes. The Veritasium demo showed MKBHD's phone sitting directly on the hardware, connected for the duration. In a real-world scenario, a pickpocket would need to hold an NFC reader against your pocket for an uncomfortable amount of time while a collaborator stands at a real terminal elsewhere.
No confirmed cases of real-world exploitation exist. In five years since disclosure, neither Apple, Visa, law enforcement, nor any fraud reporting service has documented this specific attack vector being used in the wild. That doesn't mean it hasn't happened — it means the economics of the attack (specialized hardware, coordination, physical proximity) don't scale well compared to simpler fraud methods.
The zero-liability framing is technically accurate but emotionally dishonest. If $10,000 disappeared from your account, yes, Visa's policy says you'd get it back after filing a dispute. But "you can dispute the charge" is a corporate answer to a user-experience question. The process takes days to weeks. The fraud alert might not fire immediately. And you'd have to notice the charge in the first place.
The "just disable Express Transit" fix transfers liability to the user. The researchers' recommendation since 2021 has been: don't use a Visa card for Express Transit. That's a workaround, not a fix. It means two trillion-dollar companies identified a known vulnerability in a combined product and decided the correct response was telling users to stop using a feature they shipped.
The Bigger Picture
This exploit sits at the intersection of two broader trends that should concern anyone building in fintech or mobile payments.
First, convenience features create a permanent attack surface. Express Transit was designed to solve a real UX problem — fumbling with Face ID at a crowded turnstile is annoying. But every authentication step you skip is a trust assumption you're encoding into hardware. Five years later, that assumption is still being exploited on camera by researchers, and the companies involved have decided the UX tradeoff is acceptable because the attack is "unlikely." This is the same logic pattern that produces every major breach: an edge case stays unfixed because it's "theoretical" until someone demonstrates it isn't.
Second, the Visa-only specificity reveals something about payment network architecture. Mastercard, Amex, and Discover all use different security methods for contactless transactions that prevent this exact attack. The fact that Visa's implementation is uniquely vulnerable — and has been for five years — suggests either a fundamental protocol-level weakness or a cost-benefit decision that de-prioritized fixing it. Either way, if you're integrating payment processing, the choice of card network isn't just a business relationship. It's a security posture decision.
Third, this is what responsible disclosure looks like when the vendors don't respond. The researchers tried the proper channels in 2021. Apple and Visa acknowledged the report and did nothing. Five years later, those same researchers partnered with the two largest tech YouTubers on the planet to put the exploit on camera. The Veritasium video isn't just content — it's an escalation strategy. When responsible disclosure fails, public demonstration becomes the last tool researchers have. Expect more of this pattern.
The fix is simple: go to your iPhone's Wallet settings, scroll to Transit Cards, and switch to "None" — or use a non-Visa card. It takes ten seconds.
The larger fix — the one that requires Apple or Visa to actually ship code — appears to be on nobody's roadmap.
Sources: Veritasium video demonstration · @supbrice on Threads · @firerock31 on Threads · MacRumors coverage · 9to5Mac coverage · University of Surrey original disclosure (2021) · iDropNews technical explainer · heise.de analysis